Why Pig Butchering Scams Are Effective
Why pig butchering scams are so effective — the psychology, technology, and social engineering behind crypto romance fraud.
Tactical Response
Legal tools and forensics explain how pig‑butchering works; psychology explains why it works so consistently on intelligent people. Boiler‑room operators are trained to exploit the same social engineering tactics repeatedly to gain trust and mask their intentions.
Why Smart People Fall for Pig Butchering Scams
Pig‑butchering scams succeed not because victims are naive, but because scammers systematically miscalibrate victims' assessment of risk and trust.
- Risk + trust miscalibration. Emotional closeness, daily contact, and apparent transparency (screenshots, voice notes, video calls) trick the brain into treating the scammer like a long‑time friend, so financial decisions feel safer than they objectively are.
- “Proof” that overrides intuition. Early credibility withdrawals, screenshots of profits, and references to other “clients” create a sense of evidence that drowns out lingering doubts. Victims often report ignoring their own red flags because the numbers seemed to back the story.
- Stress, loneliness, and time pressure. Scammers seek out individuals with major life stressors: divorce, illness, job loss, caregiving. These circumstances make the promise of a quick financial turnaround or emotional connection especially powerful. Scammers are trained to probe for these vulnerabilities early in their chats, then lean on them if victims begin to question their motives.
These dynamics are not happy accidents for the scammers. They help show that all pig butchering scam victims are manipulated using the same highly effective stratgies.
Social‑Engineering Tactics
One of pig butchering's most devious and effective innovations is its systematic use of social‑engineering. Chatters are highly trained and surgically skilled at creating real-seeming relationships using proven methods.
- Love‑bombing and rapid high‑trust bonding. Chatters lavish victims with intense attention, constant messages, and praise to simulate the feeling of a sudden, once‑in‑a‑lifetime connection. Their goal is to expedite their status from stranger to "partner" or "mentor" in a fraction of the time we would normally expect.
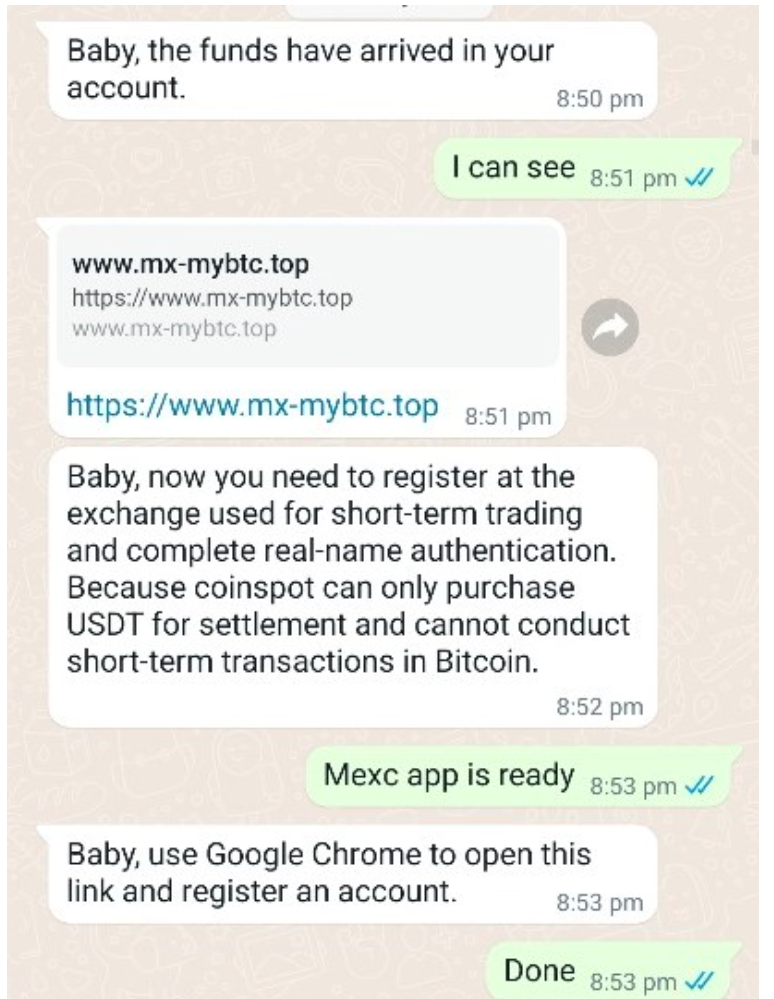
- Authority displays and borrowed status. Fake credentials, screenshots of trading dashboards, images of luxury goods and a rich lifestyle, and references to alleged mentors or "VIP groups." All of these features create a persuasive aura of expertise around the scammer. Scam rings often pull from the same quiver of fake assets repeatedly, one of the ways a trained eye can detect fraud early on.
- Scarcity and urgency. Chatters present time‑limited "windows," "exclusive strategies," and warnings that others have already seized the opportunity to push victims to act before they can consult friends, family, or professionals.
Researchers recently scoured 26 scam manuals unearthed from publicly accessible Telegram channels and found the various stages of pig butchering scams map onto seven core theories of human psychology. These tactics go beyond your run-of-the mill deception and into the realm of terrifyingly effective.
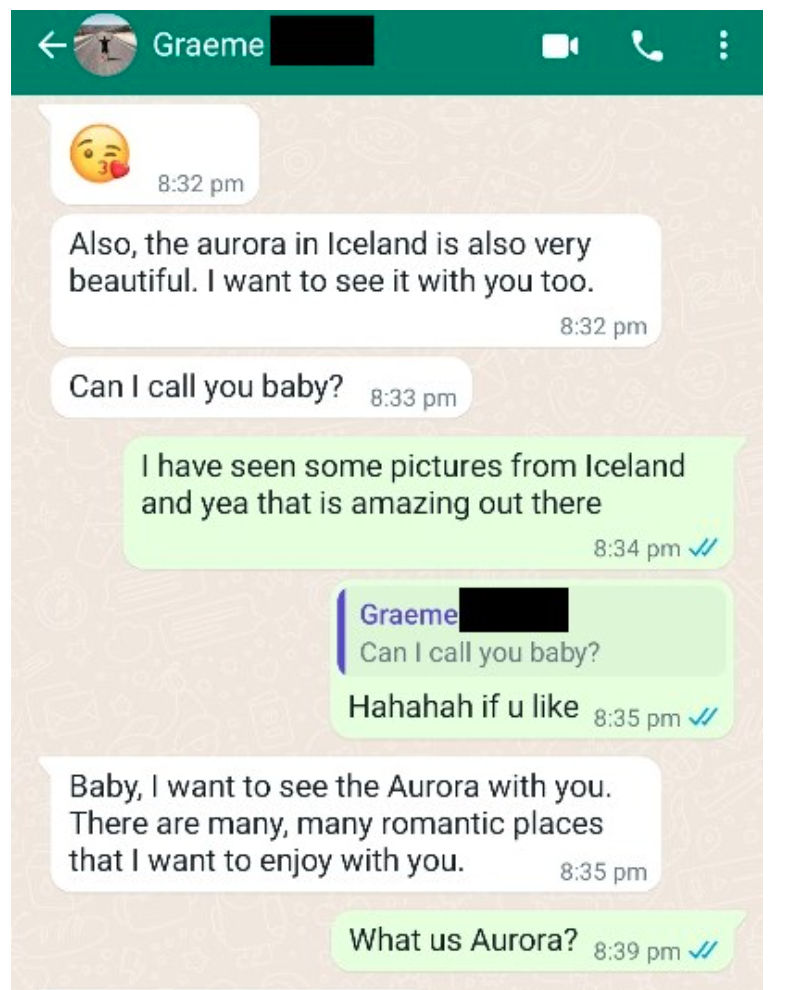
Example of love bombing tactics combined with "warm competence" tone in pig butchering scam texts.
Linguistic Patterns
Experienced investigators and crypto fraud lawyers can often recognize pig‑butchering scripts from the language alone.
- The “warm competence” voice. Messages blend affectionate nicknames and emotional support with confident, almost teacher‑like explanations of markets. The tone says “I care about you” and “I know more than you” at the same time.
- Reassurance and shared‑destiny language. Phrases about “our future,” “walking this road together,” or “not letting you miss this chance” show up across many cases, often word‑for‑word.
- Deflection and minimization. When you hesitate or raise concerns, scripts pivot to minimizing risk (“just a small test amount”), reframing caution as fear, or implying that not investing signals a lack of trust.
These repeated linguistic patterns are part of why victims describe their chats as feeling strangely “scripted” in hindsight—and why redacted transcripts can be powerful exhibits in court.
How Scammers Are Trained
Most pig‑butchering operators are trained workers following structured programs.
- Phrasebooks and script libraries. Boiler rooms maintain detailed script packets for each phase of the scam. Trainees memorize key lines, objections, and responses much like a call‑center playbook.
- Metrics and feedback loops. Operators are graded on deposits generated, conversion rates, and retention. Successful lines and tactics are copied and standardized; ineffective ones are discarded.
- Role‑playing and live supervision. New recruits often practice on low‑value targets or under supervision, with managers suggesting next lines in real time. This is one reason responses can feel both polished and oddly generic.
Understanding these tactics can help you recognize and resist them—and if you’ve already been affected, a conversation with a lawyer can help you decide your next steps.


